Akira, the ransomware that stole $42 million from more than 250 organizations worldwide

Akira, the ransomware that stole $42 million from more than 250 organizations in North America, Europe and Australia in one year, is now actively targeting businesses in Singapore.
Singaporean authorities have issued a joint warning to alert local businesses of the growing threat posed by the Akira Ransomware variant.
The alert comes after agencies including the Singapore Cyber Security Agency (CSA), the Singapore Police Force (SPF) and the Personal Data Protection Commission (PDPC) recently received several complaints from victims of cyber attack.
Main objectives of Akira ransomware
Previous investigations by the US Federal Bureau of Investigation (FBI) revealed that Akira ransomware targeted businesses and critical infrastructure entities.

Singaporean authorities have explained ways to detect, deter and neutralize Akira attacks. Companies that have been hacked are advised to refrain from paying ransom to the attackers.
Refrain from paying the ransom
Akira members are demanding payments in cryptocurrencies, such as Bitcoin (BTC), to regain control of their IT systems and internal data. However, Singaporean authorities have asked companies not to make these payments.
“If your organization’s systems have been compromised using ransomware, we do not recommend paying the ransom and advise you to report the incident to authorities immediately. Paying the ransom does not guarantee that data will be decrypted or that malicious actors will not distribute your data.
Additionally, malicious entities may attempt another attack in hopes of obtaining more ransom. The FBI discovered that Akira never contacted the victims and expected them to communicate.
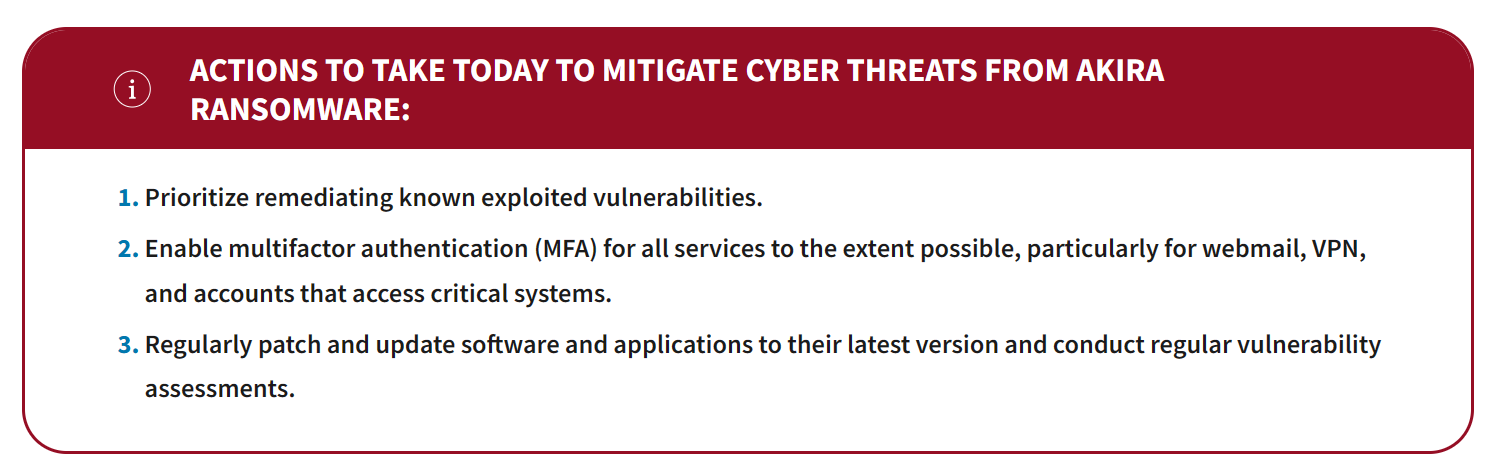
Some recommended threat mitigation techniques include implementing a recovery plan, multi-factor authentication (MFA), filtering network traffic, disabling unused ports and hyperlinks, and system-level encryption.
about: Ransomware Returns: Chaina Analysis Marks Billion Dollar Payout in 2023
Cybersecurity company Kaspersky recently discovered that North Korean hackers were targeting cryptocurrency companies in South Korea using the Dorian malware.

“Durian has full backdoor functionality, allowing for the execution of delivered orders, downloading additional files, and extracting files,” Kaspersky explained.
Additionally, Kaspersky noted that LazyLoad was also used by Andariel, a subgroup of the North Korean hacking consortium Lazarus Group, suggesting a “weak” relationship between Kimsuky and the more notorious hacking group.
review: Longevity expert: artificial intelligence will help us become “biologically immortal” from 2030